
Famous Volunteer Opportunities Richmond Va References
September 17, 2023
0 comment

Incredible Volunteer Match Mn Ideas
September 17, 2023
0 comment
Cool Volunteer Match Columbus Ohio 2023
September 14, 2023
0 comment

Incredible Volunteermatch Webinars References
September 13, 2023
0 comment

+10 Volunteer Opportunities Denver Ideas
September 12, 2023
0 comment

Incredible Volunteer Opportunities Guelph 2023
September 9, 2023
0 comment

The Best Volunteer Match Michigan 2023
September 7, 2023
0 comment

The Best Volunteer Opportunities Victoria 2023
September 6, 2023
0 comment

List Of Volunteer Opportunities Kingston References
September 5, 2023
0 comment

September 15, 2023
0 comment
'Whimsical' sculpture to honor Naperville Humane Society founders from www.dailyherald.com Are you an animal lover looking to...

Famous London Animal Shelter Volunteer References
September 14, 2023
0 comment

Famous Animal Shelter Volunteer Coordinator Job Description Ideas
September 12, 2023
0 comment

Incredible Denton Animal Shelter Volunteer Ideas
September 11, 2023
0 comment

+26 Animal Shelter Volunteer Waiver Forms 2023
September 10, 2023
0 comment

March 16, 2024
0 comment
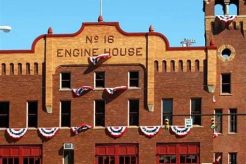
The Memphis Volunteer Fire Department is a dedicated team of courageous individuals who selflessly serve their community....
Latest Posts

April 24, 2024
0 comment
In a world marred by suffering and inequality, the work of Mercy Ships volunteer is a beacon...

Fiat Voluntas Tua: Meaning and Significance
April 24, 2024
0 comment

Library Volunteering Opportunities Near You
April 23, 2024
0 comment

Volunteers Needed for New Stadium
April 23, 2024
0 comment



















